Breach Risk Is Scored. Survival Risk Is Not.
Breach Risk Is Scored. Survival Risk Is Not.
Three displacement waves are repricing your vendor ecosystem. Your TPRM program is blind to all of them.
Your third-party risk management program can tell you whether a vendor is likely to be breached. It cannot tell you whether that vendor will remain viable, invested, and strategically committed to the product you depend on in three years.
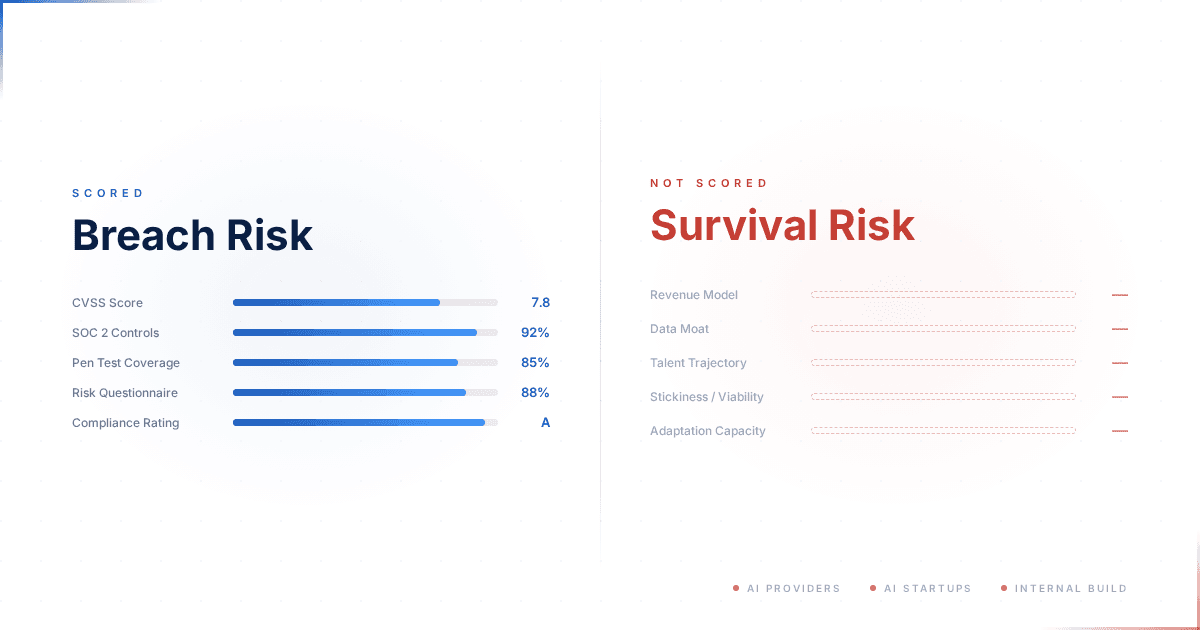
This is a gap in methodology, not execution. We have CVSS for vulnerabilities, SOC 2 for controls, penetration testing for technical exposure — an entire industry built around scoring breach probability. When the question shifts from "will they be breached?" to "will they still be building and supporting this product?" — the methodology stops. The questionnaires have no section for it. The risk register has no field.
In my assessment, for any organization running critical operations on a third-party product, this is the larger exposure. We have built rigorous process around the risk that has a recovery path and almost none around the risk that does not.
The Pattern Is Already Visible
When a security vendor suffers a data breach, your incident response plan activates. You assess exposure, notify affected parties, review controls. The vendor patches. Operations continue. This playbook exists because the industry spent two decades building it.
When that vendor's product is discontinued — no equivalent playbook exists. Operations do not pause for incident response. They degrade, lose audit traceability, and enter forced migration under time pressure that most organizations have not planned for.
This is not theoretical. Broadcom acquired CA Technologies for $18.9 billion in 2018, then Symantec's enterprise security business in 2019, then VMware for $69 billion in 2023. Each time, the post-acquisition strategy was stated publicly: focus on the highest-revenue products, deprioritize the rest. What followed across all three — portfolio rationalization, pricing restructuring, workforce reductions — was documented widely enough in trade press for the pattern to be unambiguous. By 2024, Broadcom had merged Carbon Black and Symantec into a single unit and launched a cloud-based unified platform, signaling a clear shift away from on-premises deployment. Every affected organization had SOC 2 reports, penetration test results, and completed vendor risk questionnaires. None of those instruments detected what was coming.
PE-driven restructuring produces the same blind spot differently. When Symphony Technology Group acquired FireEye's products business in 2021 and merged it with McAfee Enterprise to form Trellix — while Mandiant was separately acquired by Google — customers found themselves navigating a three-way organizational split. CRN and SC Magazine documented the integration challenges and sustained leadership turnover that followed.
A third mechanism is simpler and more abrupt. IronNet — a network detection vendor founded by a former NSA director, publicly traded at a $1.2 billion valuation in 2021 — ceased operations in September 2023 when it could no longer pay its cloud infrastructure bills. AWS shut down customer instances on September 29. The company's own filing stated it could not operate or maintain value without cloud access. Customers' collective defense coverage went dark — not from a breach, not from an acquisition, but from a vendor that ran out of cash.
Three failure modes — strategic acquisition, PE restructuring, financial collapse — same consequence: dependent organizations discovered that their risk instruments were blind to it.
These are historical patterns. What makes survival risk assessment urgent is not that vendors have failed before. It is what is about to make them fail at scale.
Three Waves of Displacement
The SaaS business model that sustains most of your vendor ecosystem is being repriced from three directions simultaneously.
Wave one: AI providers shipping the capability directly. When a foundation model can automate what a vendor prices per seat, the vendor's margin structure breaks — not because the product stops working, but because the economic logic that supports its development collapses. Charging per user for access to a capability stops making sense when the same capability becomes available at near-zero marginal cost through a platform the customer already pays for.
This stopped being theoretical on February 20, 2026, when Anthropic launched Claude Code Security — bundling security capabilities into a platform enterprises already pay for. JFrog lost nearly a quarter of its market value in a single session; Okta, CrowdStrike, and Zscaler all dropped meaningfully. Forrester's analysis was blunt: AI platforms do not need to outperform incumbents — they need only to be good enough while bundled into a product the enterprise already pays for.
Microsoft and Google are running the same play from their own platforms. IDC forecasts that 70% of software vendors will refactor away from pure per-seat pricing by 2028. The market is not waiting for 2028.
Wave two: AI-powered startups building replacements at compressed timescales. A new entrant no longer needs ten years and $200 million in venture funding to reach feature parity with an established vendor. Foundation models compress the development cycle. The capital markets have noticed: AI security startup funding nearly tripled from $2.16 billion in 2024 to $6.34 billion in 2025, with average deal sizes jumping from $34 million to $54 million. That money is flowing to teams building in months what previously took a hundred-person engineering organization years. The barrier to entry that protected incumbent vendors — accumulated engineering investment — is being devalued by the same technology that is commoditizing their output. This does not mean every startup succeeds. It means the number of credible challengers to any given vendor category is multiplying faster than incumbents can respond.
Wave three: organizations building their own. This is the displacement vector that most vendor risk assessments do not contemplate — and in my view, the one that will prove most disruptive over the next thirty-six months. Agentic AI is making it feasible for enterprises to build solutions that are adequate for their own context — not general-purpose products, not commercially viable platforms, but purpose-built capabilities that solve their specific operational problem without purchasing a vendor product at all. These can be local deployments running on the organization's own infrastructure or agent-as-a-service configurations assembled from platform components. McKinsey's 2025 cybersecurity survey found that organizations expect AI agent adoption to double within three years, with AI's share of security budgets projected to triple from 4% to 15%. That budget is not all going to vendors. The vendor does not lose to a competitor. They lose to their customer's internal capability. When the cost of building adequate-for-me drops below the cost of licensing best-in-class, the procurement decision changes — and with it, the vendor's addressable market.
These three waves operate simultaneously. None of them appears in a SOC 2 report, a vendor risk questionnaire, or a penetration test finding. The instruments that govern third-party risk today were designed for a market that no longer exists.
The Signals Hiding in Plain Sight
The signals exist. They just sit outside the instruments most organizations use.
The most predictive signal is what data sits underneath the product. Does it operate on your organization's own data, or on publicly available knowledge? A product that analyzes common vulnerability databases, maps standard compliance frameworks, or synthesizes general threat intelligence is doing work that all three displacement waves can replicate without ever touching a customer's environment. A product that operates on customer-specific operational data — your contracts, your configurations, your internal processes, your network topology — retains a structural moat against waves one and two, and a partial moat against wave three (the organization would still need to build the integration layer itself).
This is an analytical distinction, not a clean binary. Products exist on a spectrum. But it is a more reliable predictor of medium-term survivability than revenue growth or market share, because it addresses the structural question: can a differently positioned competitor — or the customer themselves — replicate your vendor's value at lower cost without needing access to your data?
Consolidation positioning is the other structural predictor. Disclosed cybersecurity M&A exceeded $76 billion in 2025. In a market consolidating at that scale, whether a vendor is positioned as a platform or a point solution matters for survival trajectory. Point solutions do not fail immediately. They get starved — of growth capital, of acquisition premium, of the investment that funds continued product development. A well-capitalized point solution with a genuine data advantage may outlast a poorly integrated platform, but the default pressure on point solutions is toward underinvestment, not growth.
Then there is the stickiness trap. Organizations routinely interpret high switching costs as evidence that a vendor relationship is safe. But stickiness and viability are independent variables. A product can be deeply embedded and declining simultaneously. The Broadcom, Trellix, and IronNet cases all demonstrate this: depth of integration did not prevent strategic change, financial collapse, or organizational restructuring. It made those events harder to escape. Complex enterprise migrations take twelve months or more. If you identify viability decline only when it becomes obvious to everyone, you are likely past the point where migration is feasible within your risk window.
The window for action closes before the urgency arrives.
Talent trajectory is the earliest warning. Engineering departures and workforce capacity decline tend to precede financial deterioration by several quarters. A vendor with stable revenue but accelerating attrition in its core engineering team is showing you its future. This does not appear in SOC 2 reports or quarterly business review slides. It is visible through LinkedIn attrition patterns, Glassdoor sentiment shifts, job posting analysis, and industry network intelligence.
Key personnel leaving is service quality degradation before it reaches the product.
Governance quality operates on a longer horizon. When executive turnover clusters, when strategic direction shifts repeatedly, when roadmap visibility decreases — these are structural signals, not noise. They tend to predict operational deterioration well before financial metrics confirm it.
What connects these signals is adaptation capacity — the vendor's ability to respond to the displacement pressures described above. Under financial stress, vendors cut R&D disproportionately. Under competitive stress from AI-native alternatives, they accelerate feature development at the expense of architectural coherence. Under customer defection to internal solutions, they raise switching costs rather than improving value. Product viability deteriorates before vendor viability does — the company survives by cutting the product's future. Financial metrics hold steady while the product enters maintenance mode.
By the time the financial picture catches up, the product has already been hollowed out.
Contracts Do Not Protect You the Way You Think
Organizations that recognize viability risk often assume their contracts handle it. Most do not.
DORA Article 28 now requires exit strategies for critical ICT third-party service providers — data portability, transition assistance, continuity planning. This is the strongest regulatory anchor for treating vendor viability as a governance obligation rather than an optional exercise. But there is a difference between holding an escrow clause and having a tested, feasible exit mechanism. Most organizations hold exit provisions they have never exercised and could not execute under time pressure.
Regulatory embedding compounds this. When a product generates audit evidence cited in regulatory submissions, when it sits inside compliance notification chains, when switching it requires re-certification — the vendor's deterioration becomes a compliance event, not just an operational one. Regulatory demand creates a viability floor for the vendor — organizations must keep buying the category — and simultaneously amplifies exit costs for the customer.
You are protected and trapped at the same time. Recognizing this dual nature is the beginning of managing it.
The Gap — and How to Close It
Breach risk scoring has institutional momentum. It maps to audit frameworks, produces quantifiable outputs, satisfies regulatory requirements. Nobody built survival risk assessment because it requires different inputs, different methods, and different outputs — and because telling a CISO that their security tooling vendor may not remain viable in its current form over thirty-six months is not a conversation anyone initiates voluntarily.
The natural response is to interpret stickiness as safety and skip the assessment.
That does not reduce exposure. It delays recognition until options have narrowed.
But the signals described in this article are observable. The methodology can be built. The assessment structure follows from the signals themselves: score vendor and product independently, because they diverge under stress. Test evidence for directional bias, because public sources skew. Surface cross-domain tensions — where one signal contradicts another — rather than smoothing them into a single score, because the contradictions are where the real risk lives.
CyberSol has released GOSTA as open source — a governance specification for autonomous AI agents that defines how multi-agent analysis sessions are structured, bounded, and audited. GOSTA is not an orchestration framework. It sits above orchestration, adding governance: what agents are permitted to decide, within what bounds, and what happens when signals contradict each other. Within GOSTA, we have published a ready-to-run vendor-product continuity assessment that operationalizes the signals described in this article. It uses eight independent domain agents — financial health, competitive displacement, SaaS viability, regulatory entrenchment, structural stickiness, adaptation capacity, governance coherence, and talent trajectory — each producing evidence-grounded position papers that challenge each other across deliberation rounds. The output is a risk determination with timeline and mitigation postures, grounded in cross-domain tensions rather than smoothed into a single score. Clone the repo, substitute your target vendor, run the session. The domain models are starting points — adapt them to your context, challenge the hypotheses, replace what does not fit. The value is in the structure of the assessment, not in any single scoring assumption.
The gap is not in the signals or the method. It is in deciding to look.
References
-
Broadcom Inc., "Broadcom to Acquire CA Technologies for $18.9 Billion in Cash," press release, July 2018. investors.broadcom.com
-
Reuters, "Broadcom to buy Symantec's enterprise unit for $10.7 billion," August 2019. reuters.com
-
Reuters, "Broadcom completes $69 billion VMware acquisition," November 2023. reuters.com
-
TechCrunch, "IronNet, founded by former NSA director, shuts down and lays off staff," October 2023. techcrunch.com
-
BankInfoSecurity, "Why IronNet Ran Out of Cash, Filed for Chapter 11 Bankruptcy," October 2023. bankinfosecurity.com
-
Forrester (Pollard, Worthington, Mellen, Burn, Nost), "Claude Code Security Causes A SaaS-pocalypse In Cybersecurity," February 2026. forrester.com
-
IDC, "Is SaaS Dead? Rethinking the Future of Software in the Age of AI," 2025. idc.com
-
Software Strategies Blog, "AI Security market 2025 funding data, top startups, and the ServiceNow factor," December 2025. softwarestrategiesblog.com
-
McKinsey & Company, "Securing the agentic enterprise: Opportunities for cybersecurity providers," 2025. mckinsey.com
-
Return on Security, "2025 State of the Cybersecurity Market," 2025. returnonsecurity.com
-
Regulation (EU) 2022/2554 (DORA), Article 28 — ICT third-party risk management. eur-lex.europa.eu
-
STG, "FireEye Announces Sale of FireEye Products Business to Symphony Technology Group for $1.2 Billion," June 2021. stg.com
-
TechCrunch, "Google closes $5.4B Mandiant acquisition," September 2022. techcrunch.com
-
SecurityWeek, "Broadcom Merges Symantec and Carbon Black Into New Business Unit," March 2024. securityweek.com
-
Bloomberg, "Anthropic Unveils 'Claude Code Security,' Sending Cyber Stocks Lower," February 2026. bloomberg.com
-
SC Magazine / CRN — coverage of Trellix integration challenges and leadership turnover, 2021–2023.
-
CyberSol, "GOSTA: An Open Governance Specification for Autonomous AI Agents," 2025. cybersol.nl
-
GOSTA-OSS repository and vendor-product continuity assessment example. github.com/cybersoloss/GOSTA-OSS